SIDs & RIDs
17.5.1 - SIDs Overview
https://learn.microsoft.com/en-us/windows-server/identity/ad-ds/manage/understand-security-identifiers
https://learn.microsoft.com/en-us/windows/win32/api/winnt/ne-winnt-well_known_sid_type
Combining information on a domain identifier and RID gives you a single ID across the entire enterprise network.
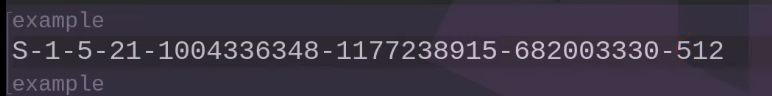
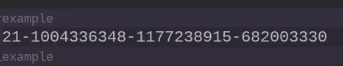
- S indicates the string is an SID
- R indicates the revision of the SID structured, that is used (usually 1)
- X determines the identifier authority that issued the SID
- & determines the subauthorities
- Long numbers identify a specific domain (21--330 in this example)
- Last part identifies a specific security principle in that domian
The SID for Contoso\Domain Admins is distinguished from the SIDs for other domain admins groups in the same enterprise by its domain identifier. Same for the Relative identifier (RID)
A list of well-known SIDs (these have an RID of under 1000). Remember we can identify domains in a specific network with this. The values of certain SIDs are constant across all systems. They're created when the OS or domain is installed and they're called well-known SIDs because they identify generic users/groups. There are universal well-known SIDs that're meaningful on all secure systems using this security model, including OS systems other than Windows. There are also well-known SIDs meaningful only on Windows OSs.
S-1-0-0 Nobody
S-1-1-0 Everybody
S-1-5-11 Authenticated Users
S-1-5-18 Local System
S-1-5-domainidentifier-500 Administrator
Enumerate all SIDs. Note all that changes is the RID.
wmic useraccount get domain, name, sid